Blog
Insights and expertise from Thoropass
Featured
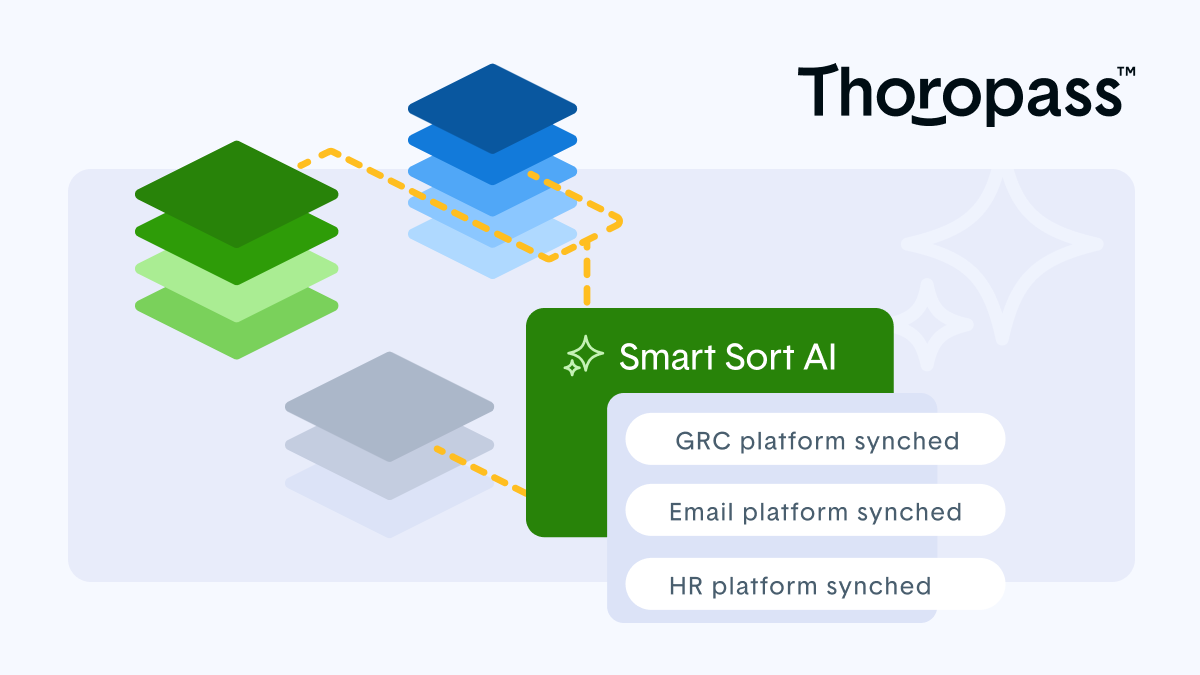
Becoming the End-to-End Cybersecurity Auditor
Innovation has always been at the forefront for Thoropass, and with the introduction of the Audit Lifecycle Platform, we're the only end-to-end cybersecurity auditor built for the AI era.
Latest posts
Compliance
What is a security controls framework?
January 2, 2026
|
Learn what a security controls framework is, how to stop duplicating evidence, and how to scale multi-framework compliance operations efficiently.
Read more
Compliance
What is a key risk indicator?
January 2, 2026
|
Learn what key risk indicators are, how they differ from KPIs, and how to
Read more
Compliance
What is residual risk?
January 2, 2026
|
Learn the specific definition of residual risk, how it differs from inherent exposure, and why modern compliance frameworks require you to track it continuously.
Read more
Compliance
What is security posture?
January 2, 2026
|
Learn what security posture is, how to measure it across your organization, and why continuous monitoring is required for modern compliance frameworks.
Read more

Compliance
What is risk register?
January 2, 2026
|
A risk register tracks identified IT threats, mitigating controls, and residual risk scores to prove continuous compliance to auditors.
Read more

Compliance
What is security architecture?
January 2, 2026
|
Learn what security architecture is, its core frameworks, and how to map
Read more
Compliance
What is risk appetite / risk tolerance?
January 2, 2026
|
Learn the difference between risk appetite and risk tolerance, and how to translate strategic board-level limits into measurable compliance metrics.
Read more

Compliance
What is compliance in cybersecurity?
January 2, 2026
|
Learn what cybersecurity compliance is, why proactive evidence collection matters, and how to map governance processes to modern regulatory enforcement frameworks.
Read more

Compliance
What is integrity in cybersecurity?
January 2, 2026
|
Learn what integrity in cybersecurity really means, how modern controls like hashing prevent tampering, and what SOC 2 or ISO 27001 auditors expect to see.
Read more
Compliance
What is defense in depth (DiD)?
January 2, 2026
|
Discover how modern defense in depth (DiD) uses deep, continuously monitored controls to block threats and simplify your compliance audits.
Read more
_%20blog%20header.png)
Compliance
What is confidentiality in cybersecurity?
January 2, 2026
|
Learn what confidentiality is in cybersecurity, how it differs from privacy, and which access controls and frameworks enforce it effectively.
Read more

Compliance
What is accountability in cybersecurity?
January 2, 2026
|
Learn what cybersecurity accountability means, how modern frameworks map risk ownership, and how to prove compliance using a formal risk register.
Read more

SOC 2
Has SOC 2 been commoditized? How to ensure your SOC 2 report helps you strengthen your posture and improve your commercial prospects
December 29, 2025
|
Leith Khanafseh
Has SOC 2 been commoditized? It depends. Here's how to ensure your SOC 2 report actually helps you strengthen your security posture.
Read more
ISO 42001
Responsible AI usage: where to begin for security leaders
November 18, 2025
|
Thoropass Team
Getting a handle on AI usage in your organization can be challenging. Learn more about how to get started.
Read more
Curated by experts
We provide the compliance expertise, so you don’t have to
At Thoropass, we’re more than a readiness solution. Our team of experts are equipped with insight and hands-on experience to provide you with industry-leading perspective and guidance.
Meet the Experts
Stay connected
Subscribe to receive new blog articles and updates from Thoropass in your inbox.
Oops! Something went wrong while submitting the form.
Want to join our team?
Help Thoropass ensure that compliance never gets in the way of innovation.
View open roles










.png)